Wazuh
Wazuh is a free, open-source security platform that unifies threat detection, security monitoring, incident response, and compliance in a single solution. The platform provides comprehensive security capabilities for endpoints, cloud environments, and container infrastructures.
The following are trademarks of their respective owners: Wazuh (Wazuh Inc.). WZ-IT is an independent service provider and has no business, partnership, or contractual relationship with these companies. We offer independent migration, installation, hosting, and operations services.
About Wazuh
Wazuh is a free, open-source security platform that unifies threat detection, security monitoring, incident response, and compliance in a single solution. The platform provides comprehensive security capabilities for endpoints, cloud environments, and container infrastructures.
As an experienced Wazuh partner, we support you in installing, configuring, and integrating this powerful security platform into your existing IT infrastructure to meet your security and compliance requirements.
Why Wazuh with WZ-IT?
We install, host and operate Wazuh for your company - either on our secure, GDPR-compliant infrastructure in Germany or other locations, as well as on-premise in your own environment.
With 24/7 monitoring, enterprise support, backups and professional maintenance, we ensure maximum availability and reliable operation of your Wazuh instance.
Configuration Assessment
Monitoring of system and application configurations for compliance with security policies and automatic detection of misconfigurations.
Malware Detection
Identification of malicious activities and indicators of compromise through integrated rule sets and specialized detection capabilities.
File Integrity Monitoring
Continuous monitoring of the file system to detect changes in content, permissions, and attributes of critical files.
Threat Hunting
Comprehensive visibility into monitored endpoints, log indexing and querying, and integration with MITRE ATT&CK for effective threat analysis.
Vulnerability Detection
Automated detection of known vulnerabilities by correlating software inventory data with continuously updated CVE databases.
Compliance Management
Integrated security controls for compliance with industry standards and regulations such as PCI DSS, NIST, TSC, and HIPAA with specialized reports.
Wazuh in Action
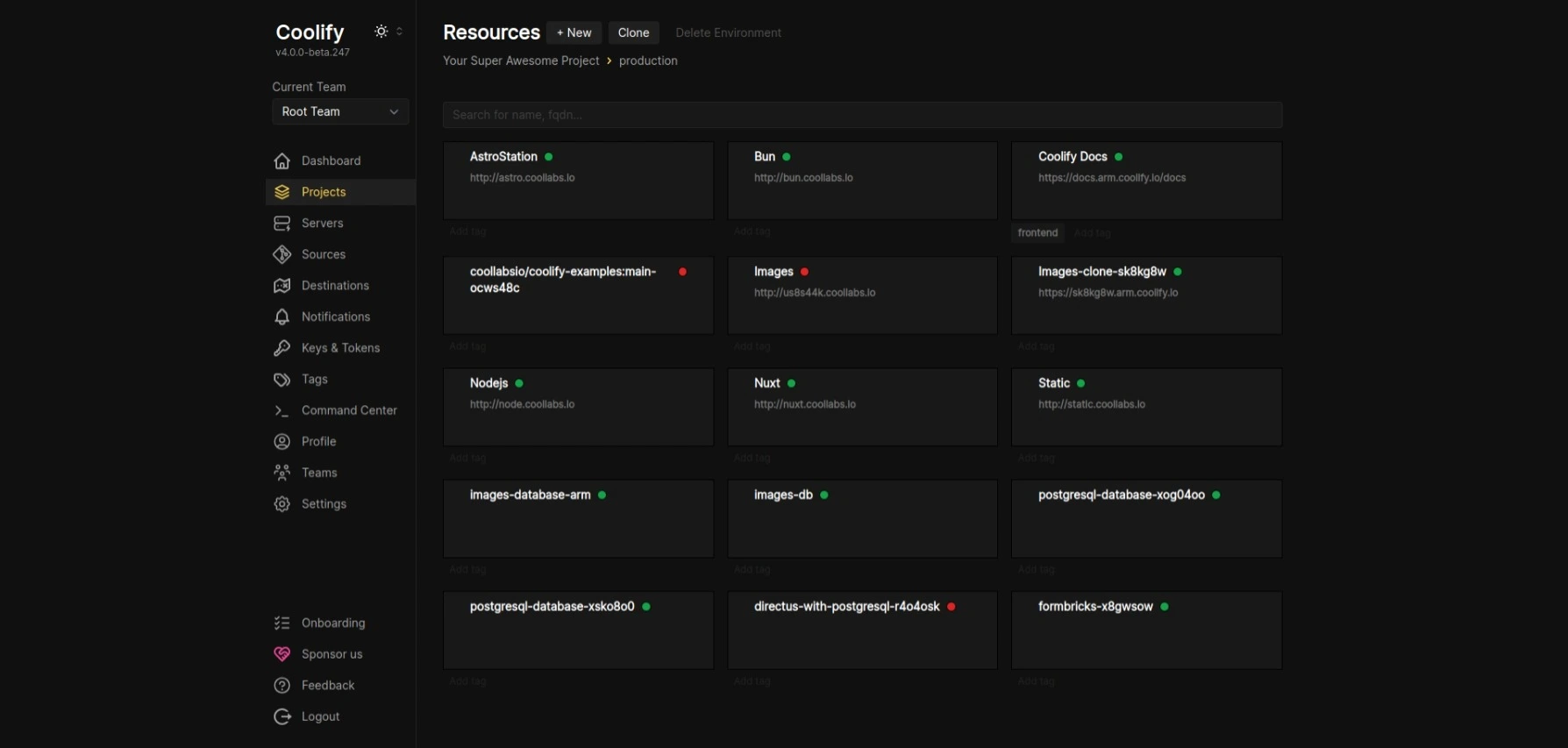
Experience Wazuh in Action
See how simple and efficient Wazuh works in practice. From installation to productive use.
Wazuh Installation & Einrichtung
Professional installation on your infrastructure – on-premise, cloud or hybrid
On-Premise
In your data center
- Installation on bare-metal, VM or Docker
- Optimal performance configuration
- Integration with existing Active Directory/LDAP
- SSL certificate & reverse proxy
- Backup strategy & monitoring
- Security hardening following best practices
- Documentation & training
Cloud Installation
AWS, Azure, Hetzner & more
- Installation on AWS, Azure, GCP, Hetzner
- Terraform/IaC setup (optional)
- Kubernetes or Docker Compose
- Auto-scaling configuration
- Load balancer & CDN integration
- CloudWatch/monitoring setup
- Cost optimization & best practices
Enterprise Setup
High-availability setup with comprehensive security and compliance features
- High-availability cluster setup
- VPN access (e.g. WireGuard, NetBird, Tailscale)
- SSO integration (e.g. Keycloak, Authentik, Azure AD)
- Multi-factor authentication (MFA)
- Audit logging & compliance
- Disaster recovery plan
- Custom security policies
- Dedicated contact person
Security & Secure Access
Secure access and access control for your installation
VPN Access
WireGuard, NetBird or Tailscale
SSO Integration
Keycloak, Authentik, Azure AD
Multi-Factor Auth
TOTP, WebAuthn, YubiKey
Firewall & Hardening
Fail2Ban, Rate Limiting, IP Whitelisting
Secure Access via VPN
We set up secure VPN access to your installation – ideal for remote work and external employees.
- Zero-Trust Network Access (ZTNA)
- Encrypted connections
- Easy client setup for all devices
- Centralized access management
Supported VPN Solutions:
What's Included in the Service
Full-service installation with no hidden costs
Wazuh Development & Integration
Wazuh only becomes powerful through customization. We transform it from a passive log collector into an active defense system via custom engineering.
Custom Decoders (RegEx)
Standard logs are recognized, but your proprietary app? We write complex RegEx decoders to convert logfiles from your business apps into structured security events.
Active Response Scripts
Attack detected -> script executed. We develop Python/Bash scripts for Active Response: blocking IPs in firewall, disabling users, or isolating containers.
API Integration
Integration with ticket systems (Jira/Zammad). High-severity alerts automatically create an incident ticket with all forensic data.
Concrete Use Cases
How we implement Wazuh development in practice.
GDPR/ISO Compliance Rules
Standard rulesets do not cover specific compliance requirements.
Development of custom rules monitoring access to PII data and alerting immediately on anomalies.
Ransomware Killswitch
Manual response to ransomware behavior is too slow.
Active Response logic that immediately disables the network adapter of the affected server upon mass file changes (encryption behavior).
Enterprise Managed Hosting
Enterprise Grade
Open source enterprise-ready for productive workloads - we run your applications with highest security standards and enterprise support
Why Enterprise Managed Hosting?
Open source software for business-critical processes requires professional maintenance, continuous updates, and enterprise-grade support. With our Wazuh Enterprise Managed Hosting, you get the necessary infrastructure and support to reliably operate open source in production environments. Backups, SLAs, telephone support, and personal contact - so you can focus on your core business.
Installation on Your Infrastructure
Looking for a custom solution?
We also offer customized Wazuh Enterprise solutions for your specific requirements. Contact us for an individual quote.
Interested in Wazuh?
Good choice - we'll help you get started or with operations.
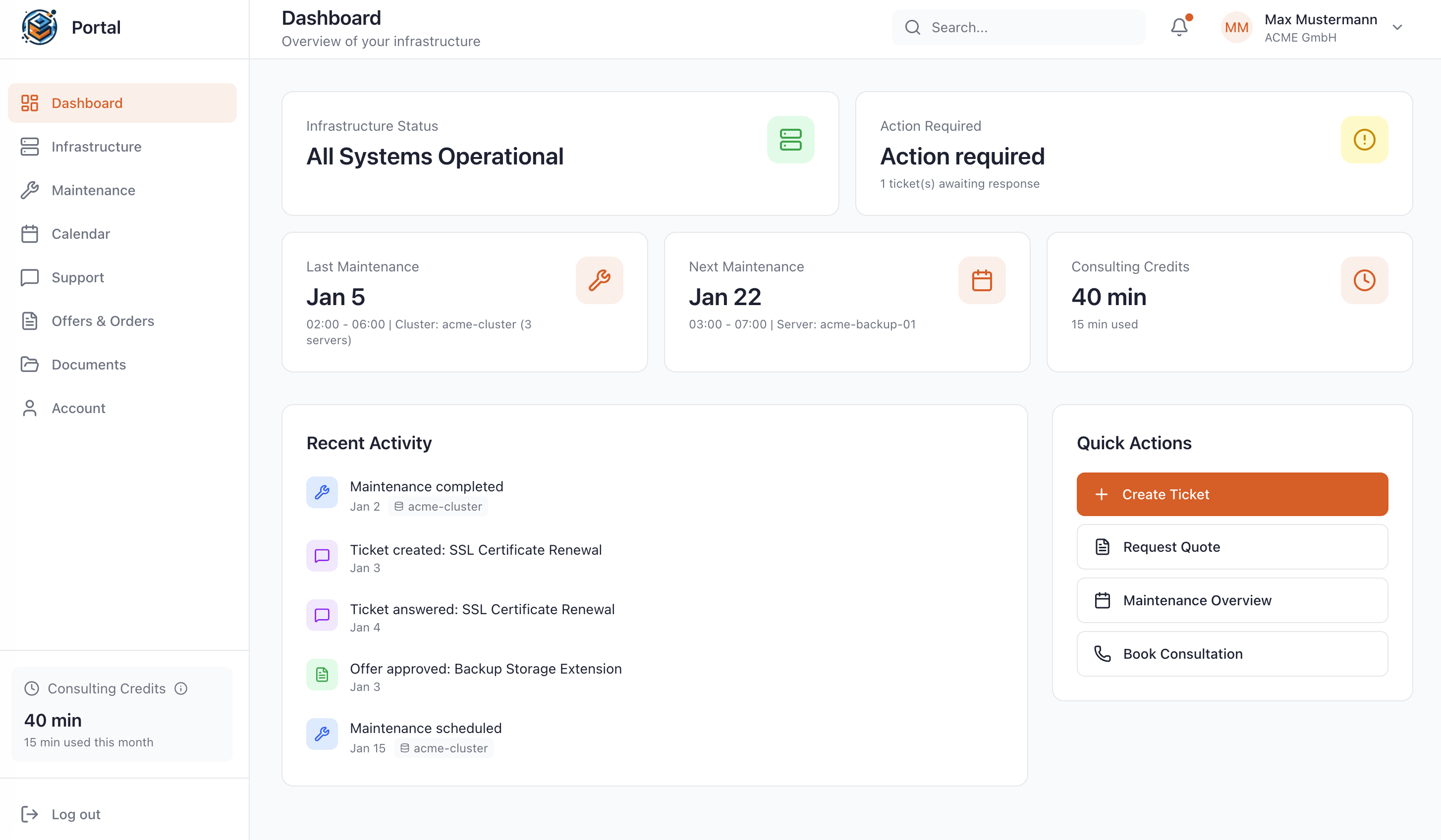
Manage Your Stack in the Customer Portal
As a Managed Service customer at WZ-IT, you have access to our exclusive portal: Monitor your infrastructure in real-time, schedule maintenance, request quotes, and get direct support - all in one central location.
- Real-time infrastructure status
- Reschedule maintenance windows yourself
- View complete access logs
- Direct support without detours
Matching Solutions for Your Project
Complementary Technologies
These solutions are often used together with Wazuh
Similar Technologies
These solutions offer similar functionalities and can be evaluated together
Let's Talk About Your Idea
Whether a specific IT challenge or just an idea - we look forward to the exchange. In a brief conversation, we'll evaluate together if and how your project fits with WZ-IT.

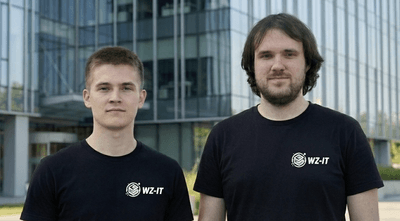
Timo Wevelsiep & Robin Zins
Managing Directors of WZ-IT