Keycloak
Keycloak is a leading open-source solution for Identity and Access Management (IAM). With Keycloak, you can add authentication and authorization to applications without having to deal with storing users or authenticating users.
What is Keycloak?
Keycloak is a leading open-source solution for Identity and Access Management (IAM). With Keycloak, you can add authentication and authorization to applications without having to deal with storing users or authenticating users.
As a Cloud Native Computing Foundation project, Keycloak provides Single Sign-On, user management, fine-grained authorization, and comprehensive integration with existing directory services like LDAP and Active Directory.
Ready for Keycloak?
We install, host and operate Keycloak for your company - either on our secure, GDPR-compliant infrastructure in Germany or other locations, as well as on-premise in your own environment.
With 24/7 monitoring, enterprise support, backups and professional maintenance, we ensure maximum availability and reliable operation of your Keycloak instance.
Single Sign-On (SSO)
Users authenticate once with Keycloak and automatically have access to all connected applications.
Standard Protocols
Full support for OpenID Connect, OAuth 2.0, and SAML 2.0 for maximum compatibility.
User Federation
Native integration with LDAP and Active Directory plus support for custom user stores.
Identity Brokering
Easy integration with external identity providers and social login providers like Google, Facebook, GitHub.
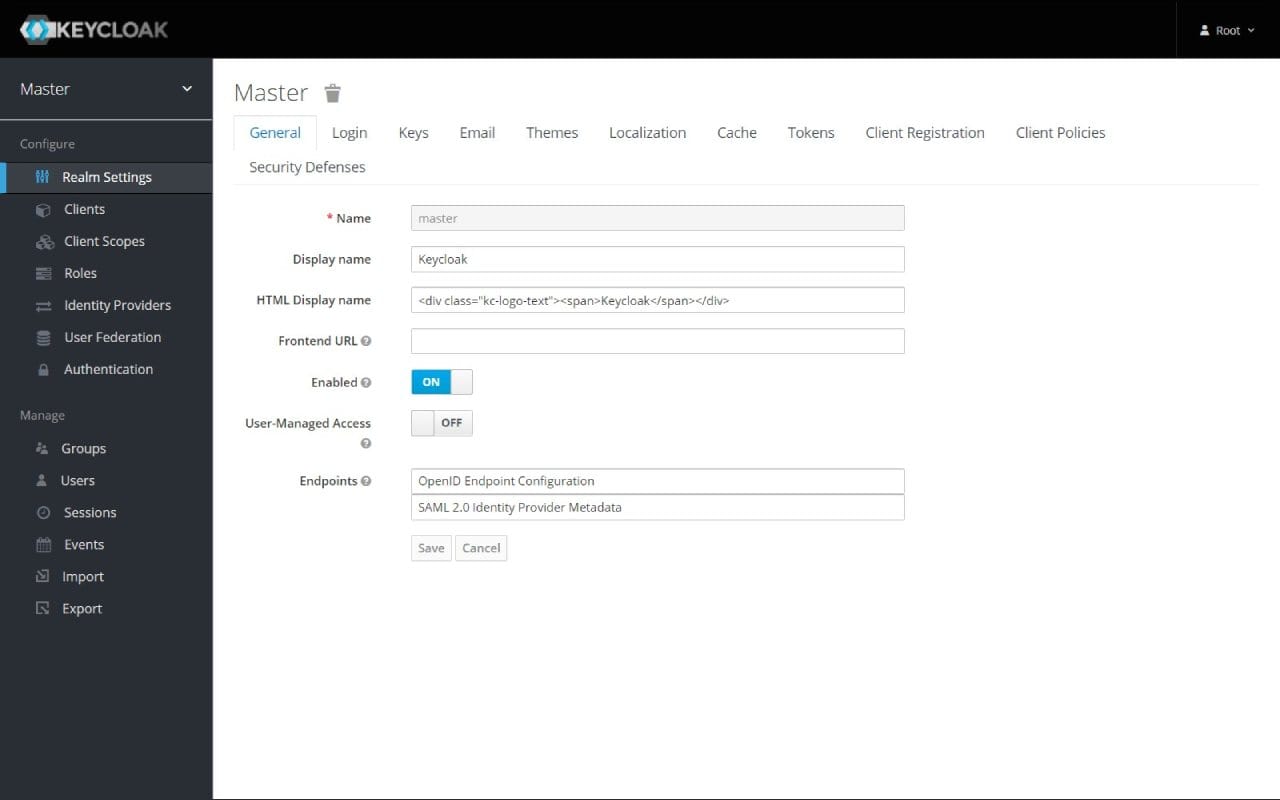
Admin Console
Centralized web-based management of all aspects of Keycloak, applications, users, and policies.
Fine-Grained Authorization
Advanced authorization services with role-based and policy-based access control mechanisms.
Account Management
Self-service portal for users to manage their profiles, passwords, and two-factor authentication.
High Performance
Lightweight, fast, and scalable with clustering support for high availability.
Customizable & Extensible
Themes for custom designs, extensive APIs and SPI for tailored extensions.
Keycloak in Action
Experience Keycloak in Action
See how simple and efficient Keycloak works in practice. From installation to productive use.
Keycloak Installation & Einrichtung
Professional installation on your infrastructure – on-premise, cloud or hybrid
On-Premise
In your data center
- Installation on bare-metal, VM or Docker
- Optimal performance configuration
- Integration with existing Active Directory/LDAP
- SSL certificate & reverse proxy
- Backup strategy & monitoring
- Security hardening following best practices
- Documentation & training
Cloud Installation
AWS, Azure, Hetzner & more
- Installation on AWS, Azure, GCP, Hetzner
- Terraform/IaC setup (optional)
- Kubernetes or Docker Compose
- Auto-scaling configuration
- Load balancer & CDN integration
- CloudWatch/monitoring setup
- Cost optimization & best practices
Enterprise Setup
High-availability setup with comprehensive security and compliance features
- High-availability cluster setup
- VPN access (e.g. WireGuard, NetBird, Tailscale)
- SSO integration (e.g. Keycloak, Authentik, Azure AD)
- Multi-factor authentication (MFA)
- Audit logging & compliance
- Disaster recovery plan
- Custom security policies
- Dedicated contact person
Perfekt für diese Anwendungsfälle
Enterprise Single Sign-On
Centralized authentication for all enterprise applications with SAML, OAuth 2.0 and OpenID Connect
Identity & Access Management
Comprehensive IAM with user and role management, fine-grained authorization and access control
Social Login Integration
Integration with Google, GitHub, LinkedIn, Microsoft and other social identity providers
Multi-Factor Authentication
2FA/MFA with OTP, WebAuthn, FIDO2 and hardware tokens for enhanced security
API Security
OAuth 2.0 and OpenID Connect for secure API access and service-to-service communication
LDAP/AD Integration
Seamless integration with existing Active Directory and LDAP directory services
Security & Secure Access
Secure access and access control for your installation
VPN Access
WireGuard, NetBird or Tailscale
SSO Integration
Keycloak, Authentik, Azure AD
Multi-Factor Auth
TOTP, WebAuthn, YubiKey
Firewall & Hardening
Fail2Ban, Rate Limiting, IP Whitelisting
Secure Access via VPN
We set up secure VPN access to your installation – ideal for remote work and external employees.
- Zero-Trust Network Access (ZTNA)
- Encrypted connections
- Easy client setup for all devices
- Centralized access management
Supported VPN Solutions:
What's Included in the Service
Full-service installation with no hidden costs
Keycloak Development & Integration
Keycloak is modular to the core. Almost every functionality is a replaceable provider. We use Java to implement these SPIs and adapt Keycloak exactly to your infrastructure.
User Storage SPI
The most important point: We don't necessarily migrate your users. We develop User Storage Providers allowing Keycloak to read users directly from your existing SQL DB, mainframe, or API – without duplication.
Event Listener SPI
Audit compliance requires gapless logs. We write Event Listeners that stream every login, error, and admin action to your SIEM (Splunk, ELK, Graylog) in real-time.
Custom Themes (Freemarker)
The standard login window is off-putting. We develop responsive, accessible themes (based on your CI/CD) that seamlessly integrate the login experience into your application.
Concrete Use Cases
How we implement Keycloak development in practice.
Federation with Legacy Systems
You have thousands of users in an old MySQL database of an EOL software that cannot be migrated.
A 'read-only' User Storage SPI connects the old DB. Keycloak authenticates against old hashes but issues modern OAuth2/OIDC tokens for new apps.
Passwordless Auth & Magic Links
B2C customers constantly forget passwords. The login process must be frictionless.
Implementation of a custom authentication flow that only asks for emails and sends magic links. Fully integrated into Keycloak core, secure, and audited.
Token Enrichment (Mappers)
Your application needs specific data in the JWT (e.g., tenant ID, cost center) not found in LDAP.
A Script Mapper (JavaScript) or Protocol Mapper (Java) loads this data from an external API during login and signs it into the access token.
Enterprise Managed Hosting
Enterprise Grade
Open source enterprise-ready for productive workloads - we run your applications with highest security standards and enterprise support
Why Enterprise Managed Hosting?
Open source software for business-critical processes requires professional maintenance, continuous updates, and enterprise-grade support. With our Keycloak Enterprise Managed Hosting, you get the necessary infrastructure and support to reliably operate open source in production environments. Backups, SLAs, telephone support, and personal contact - so you can focus on your core business.
Installation on Your Infrastructure
Looking for a custom solution?
We also offer customized Keycloak Enterprise solutions for your specific requirements. Contact us for an individual quote.
Interested in Keycloak?
Good choice – we'll help you get started or with operations.
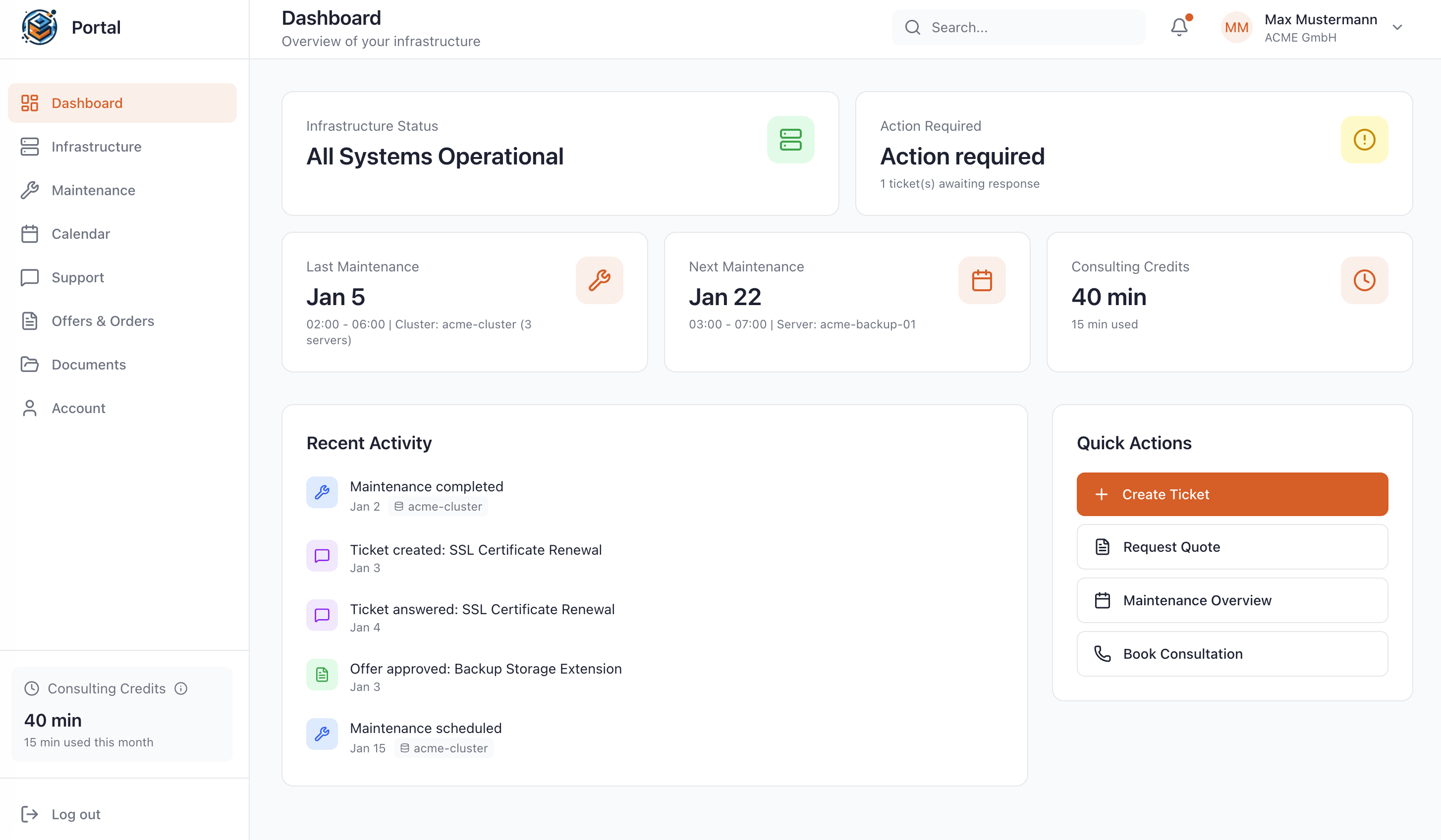
Manage Your Stack in the Customer Portal
As a Managed Service customer at WZ-IT, you have access to our exclusive portal: Monitor your infrastructure in real-time, schedule maintenance, request quotes, and get direct support – all in one central location.
- Real-time infrastructure status
- Reschedule maintenance windows yourself
- View complete access logs
- Direct support without detours
Matching Solutions for Your Project
Complementary Technologies
These solutions are often used together with Keycloak
Similar Technologies
These solutions offer similar functionalities and can be evaluated together
Alternative Solutions
These solutions are direct alternatives with similar use cases
Let's Talk About Your Idea
Whether a specific IT challenge or just an idea – we look forward to the exchange. In a brief conversation, we'll evaluate together if and how your project fits with WZ-IT.

Timo Wevelsiep & Robin Zins
CEOs of WZ-IT