Authentik
Authentik is a modern, flexible identity provider solution designed for self-hosting. With complete control over your identity data, Authentik offers comprehensive Identity & Access Management capabilities for organizations of any size.
What is Authentik?
Authentik is a modern, flexible identity provider solution designed for self-hosting. With complete control over your identity data, Authentik offers comprehensive Identity & Access Management capabilities for organizations of any size.
As a Zero Trust Gateway, Authentik implements granular access control based on user identity, device, location, and behavior. The solution supports modern standards like OAuth2, OpenID Connect, SAML2 and provides seamless integration into existing infrastructures.
Ready for Authentik?
We install, host and operate Authentik for your company - either on our secure, GDPR-compliant infrastructure in Germany or other locations, as well as on-premise in your own environment.
With 24/7 monitoring, enterprise support, backups and professional maintenance, we ensure maximum availability and reliable operation of your Authentik instance.
Self-host Anywhere
Run Authentik on your own infrastructure (Docker, Kubernetes, etc.) for complete control over your identity data.
Single Sign-On (SSO)
Unified login processes across all applications with support for industry-standard protocols.
Multi-factor Authentication
Comprehensive MFA support with TOTP, WebAuthn/Passkeys in hardware or software for maximum security.
Conditional Access Control
Granular policies based on user attributes, time, location, and more for precise access control.
FIDO2 & Passkey Support
Passwordless authentication using FIDO2 standards for a secure, phishing-resistant login experience.
Zero Trust Architecture
Implementation of Zero Trust principles with fine-grained access controls and continuous verification.
GeoIP & Impossible Travel Detection
Detection of suspicious login attempts based on GeoIP location and travel patterns to prevent unauthorized access.
Comprehensive Audit Logging
Track changes with field-level details for comprehensive security monitoring and compliance.
Comprehensive Protocol Support
OAuth2/OpenID Connect, SAML2, LDAP, RADIUS, and SCIM for seamless integration into existing systems.
Authentik in Action
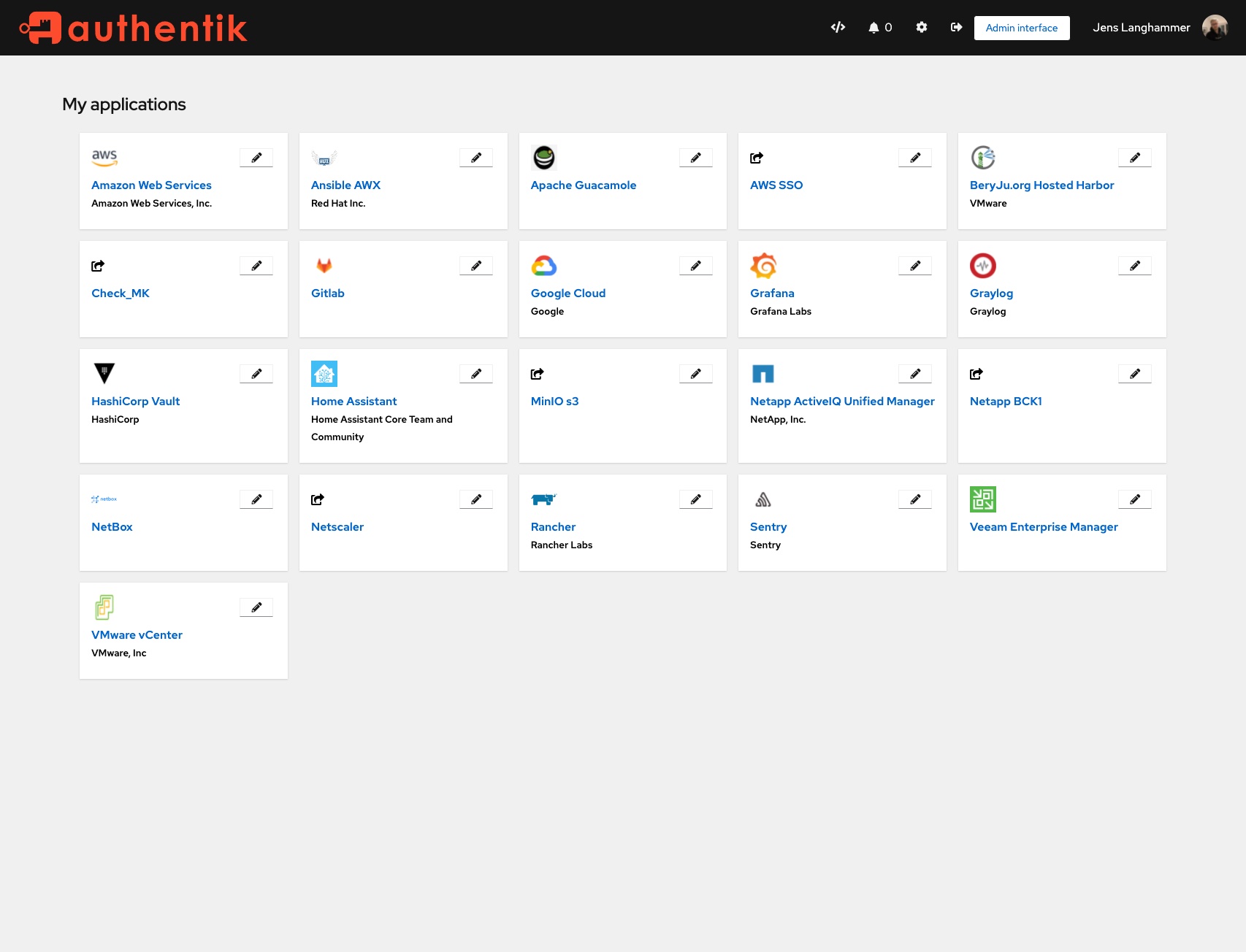
Experience Authentik in Action
See how simple and efficient Authentik works in practice. From installation to productive use.
Authentik Installation & Einrichtung
Professional installation on your infrastructure – on-premise, cloud or hybrid
On-Premise
In your data center
- Installation on bare-metal, VM or Docker
- Optimal performance configuration
- Integration with existing Active Directory/LDAP
- SSL certificate & reverse proxy
- Backup strategy & monitoring
- Security hardening following best practices
- Documentation & training
Cloud Installation
AWS, Azure, Hetzner & more
- Installation on AWS, Azure, GCP, Hetzner
- Terraform/IaC setup (optional)
- Kubernetes or Docker Compose
- Auto-scaling configuration
- Load balancer & CDN integration
- CloudWatch/monitoring setup
- Cost optimization & best practices
Enterprise Setup
High-availability setup with comprehensive security and compliance features
- High-availability cluster setup
- VPN access (e.g. WireGuard, NetBird, Tailscale)
- SSO integration (e.g. Keycloak, Authentik, Azure AD)
- Multi-factor authentication (MFA)
- Audit logging & compliance
- Disaster recovery plan
- Custom security policies
- Dedicated contact person
Perfekt für diese Anwendungsfälle
Enterprise SSO
Single Sign-On for all your enterprise applications with centralized authentication and authorization
Zero Trust Security
Conditional access and risk-based authentication for modern security architectures
Passwordless Authentication
FIDO2, WebAuthn and Passkey support for secure and user-friendly login without passwords
Identity Management
Centralized user management with LDAP and Directory Sync for seamless integration
Multi-Protocol Support
OAuth2, SAML, LDAP and SCIM in one solution for maximum compatibility
Compliance & Audit
Complete audit logs and compliance reports for regulated industries
Security & Secure Access
Secure access and access control for your installation
VPN Access
WireGuard, NetBird or Tailscale
SSO Integration
Keycloak, Authentik, Azure AD
Multi-Factor Auth
TOTP, WebAuthn, YubiKey
Firewall & Hardening
Fail2Ban, Rate Limiting, IP Whitelisting
Secure Access via VPN
We set up secure VPN access to your installation – ideal for remote work and external employees.
- Zero-Trust Network Access (ZTNA)
- Encrypted connections
- Easy client setup for all devices
- Centralized access management
Supported VPN Solutions:
What's Included in the Service
Full-service installation with no hidden costs
Authentik Development & Integration
Authentik is extremely flexible because every authentication step is a 'stage' in a 'flow'. We use Python to inject logic directly into these flows.
Expression Policies (Python)
Instead of rigid rules, we write Python code for policies. Access only if user is in office (IP range) AND shift plan API reports 'active'? No problem. We integrate external APIs directly into the auth decision.
Custom Flow Stages
When standard stages (MFA, password) aren't enough, we develop custom stages. For example, querying a proprietary hardware token database or legal disclaimer confirmation with versioning.
Blueprints & IaC
We don't configure Authentik manually. We define your complete IAM logic as code (Blueprints). This allows reproducible setups for Dev/Staging/Prod and disaster recovery.
Concrete Use Cases
How we implement Authentik development in practice.
Legacy System Migration
User passwords are in an old Oracle DB with proprietary hash algorithm. Resetting all passwords is not an option.
A custom password stage checks login attempts against the old database. Upon success, Authentik transparently migrates the user and re-hashes the password to modern standards.
Dynamic Permissions
Group membership alone is insufficient. Permissions depend on project status or certifications stored in third-party systems.
A policy queries your HR API or project software upon login and dynamically injects permissions as claims into the OIDC/SAML token.
Specialized MFA Methods
TOTP or WebAuthn aren't possible (e.g., in high-security areas without smartphones), smartcards or matrix cards are used instead.
Implementation of a custom MFA stage mapping the challenge-response logic of your physical tokens.
Enterprise Managed Hosting
Enterprise Grade
Open source enterprise-ready for productive workloads - we run your applications with highest security standards and enterprise support
Why Enterprise Managed Hosting?
Open source software for business-critical processes requires professional maintenance, continuous updates, and enterprise-grade support. With our Authentik Enterprise Managed Hosting, you get the necessary infrastructure and support to reliably operate open source in production environments. Backups, SLAs, telephone support, and personal contact - so you can focus on your core business.
Installation on Your Infrastructure
Looking for a custom solution?
We also offer customized Authentik Enterprise solutions for your specific requirements. Contact us for an individual quote.
Interested in Authentik?
Good choice – we'll help you get started or with operations.
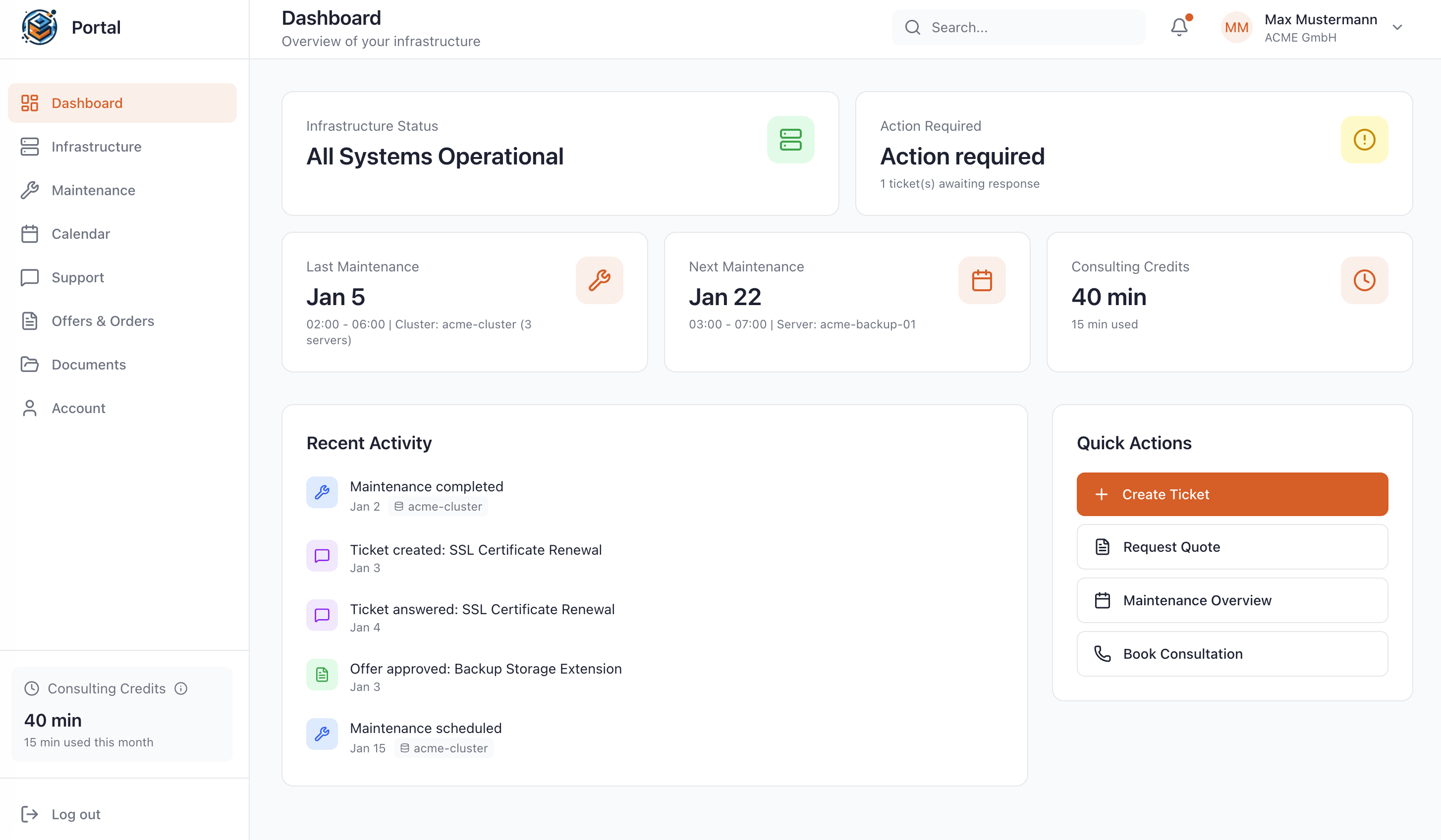
Manage Your Stack in the Customer Portal
As a Managed Service customer at WZ-IT, you have access to our exclusive portal: Monitor your infrastructure in real-time, schedule maintenance, request quotes, and get direct support – all in one central location.
- Real-time infrastructure status
- Reschedule maintenance windows yourself
- View complete access logs
- Direct support without detours
Matching Solutions for Your Project
Complementary Technologies
These solutions are often used together with Authentik
Similar Technologies
These solutions offer similar functionalities and can be evaluated together
Alternative Solutions
These solutions are direct alternatives with similar use cases
Let's Talk About Your Idea
Whether a specific IT challenge or just an idea – we look forward to the exchange. In a brief conversation, we'll evaluate together if and how your project fits with WZ-IT.

Timo Wevelsiep & Robin Zins
CEOs of WZ-IT